|
May 2022
AutomatedBuildings.com
|
[an error occurred while processing this directive]
(Click
Message to Learn More)
|
There
are hundreds of articles written about the cyber security of Building
Management Systems, but the topic is so immense that there is always a place
for discussion. All major players are trying to be one step ahead both of cybercriminals
and competition.
Niagara Framework proved to be a
leader in this area. Let’s see why.
New
versions of Niagara are not annoying, they are exciting! When we get a phone
software update we typically have no idea what this update is going to give us,
that’s why when you get a few of those updates during a shorter period they can
become annoying. The only way to avoid that is to give the customer what they
wanted, needed and asked for. Especially if it is related to security. From my
experience that is what Tridium does with new Niagara versions. If we go
through the historical changes, which were introduced with every new version,
we can see the system’s security evolution.
For
example, when the 4.8 version was released, we were able to see that Niagara
did apply industry best practices for cyber security. The support of such
features as strong, hashed passwords, TLS for secure communications and
certificate management tools for authentication was a significant part of the
system’s security. Besides that, a built-in Security Dashboard provided a
comprehensive and actionable view of the security status of every Niagara
deployment. Our clients were given an easy overview of how their system is
evaluated according to security standards. That’s what Google does with our
google accounts. When you know your weak spots you can work on strengthening
them.
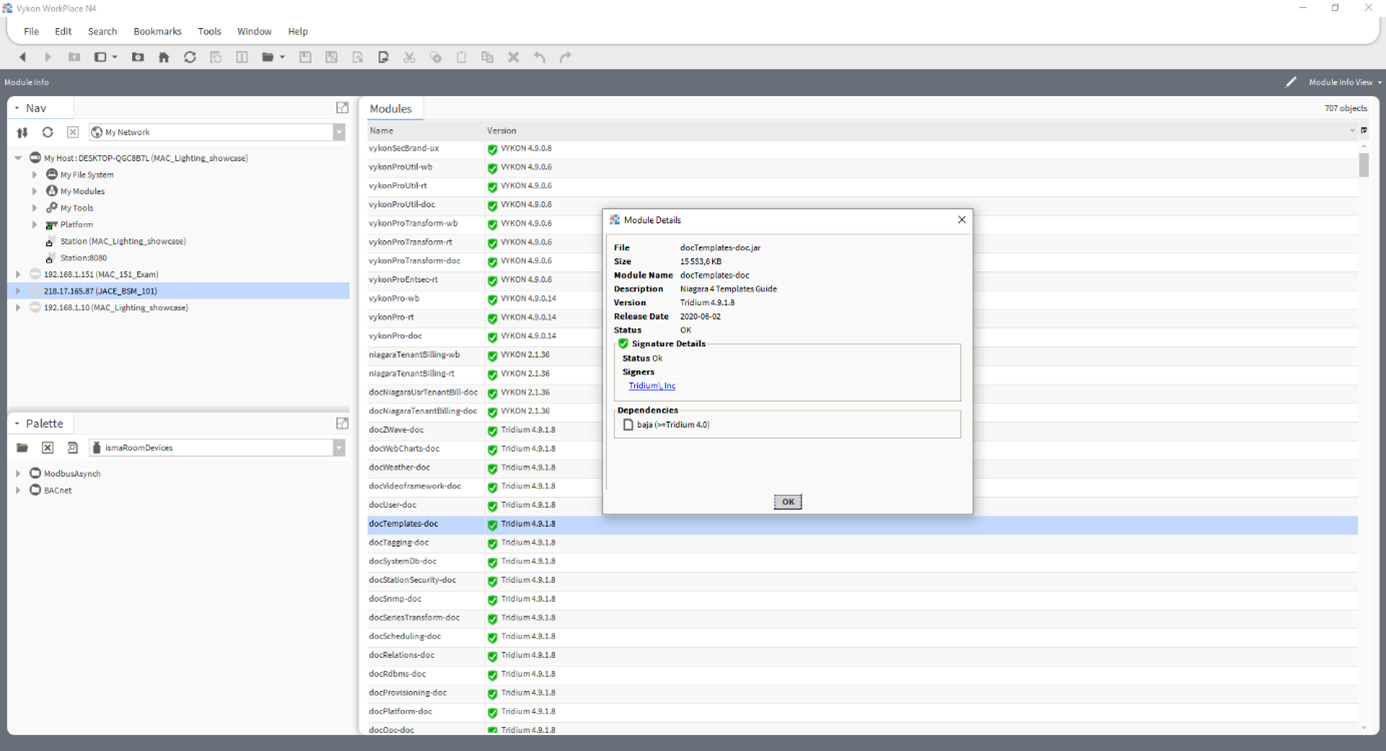
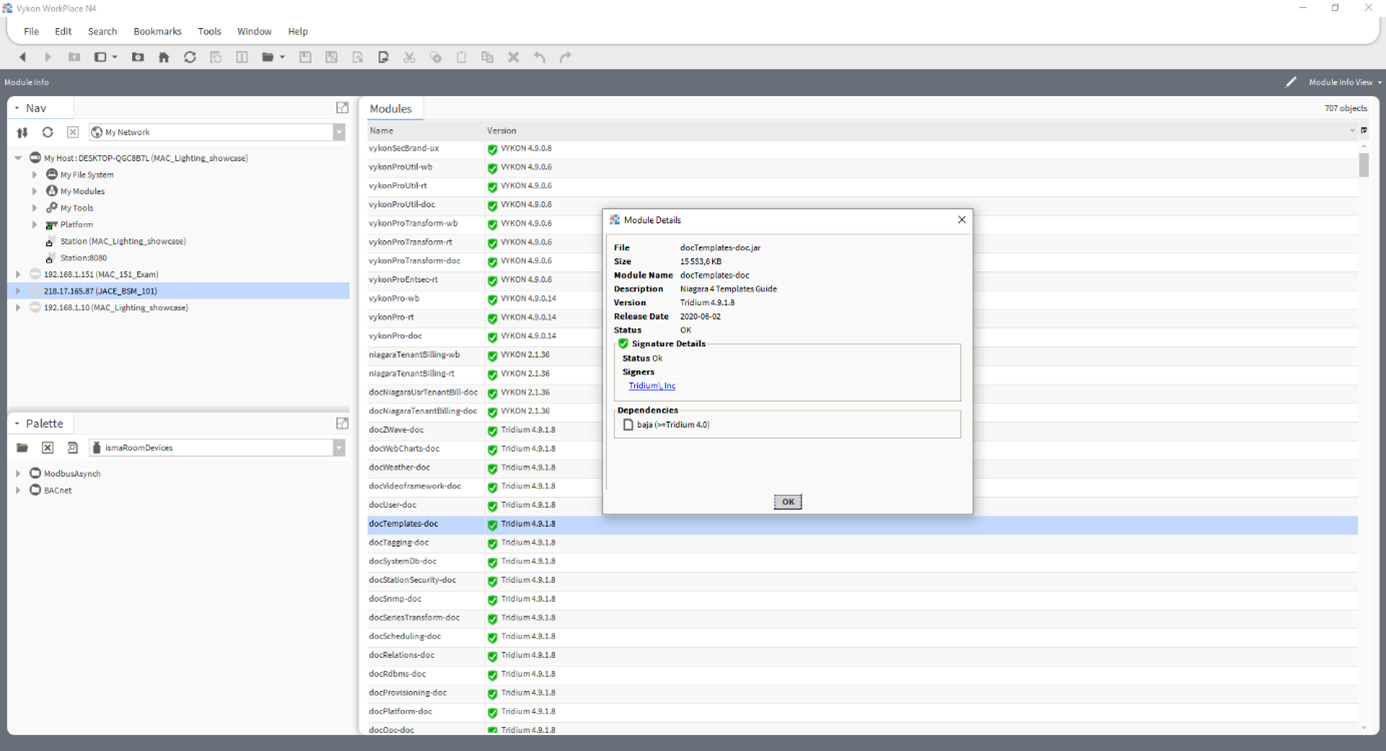
With
the introduction of the Niagara 4.9 version, it was nice to see that the system
become eligible for accreditation under the Federal Risk Management Framework
(RMF). This information assures us that the security standards are analysed
according to United States federal government guidelines, standards and processes
for risk management. The FIPS 140-2 Level 1 conformance become available as
well, approving that the first requirements regarding standards for
cryptography modules were met. Also, we
got significant changes regarding Module Signing Requirements. The new version got ‘Medium’ module
verification mode by default. That means that modules must be signed by a
trusted certificate, self-signed certificates are still acceptable, but must be
installed in a user trust store. This by default increased the security of the
system, compared to previous versions.
With
Niagara 4.11 we got improvement in BACnet communication, which is one of the
most commonly used protocols in BAS. Users got a BACnet Secure Connect which
simplifies the configuration of network parameters while enhancing security. One
of the major differences was the introduction of the TLS1.3 standard for
communications over IP.
All
these steps are building confidence in our clients that the system they are
selecting is safe and the Tridium team is constantly fixing potential vulnerabilities
in Niagara Framework.
Of
course, the BMS system itself will not provide full cyber security protection. We
know from statistics that the human factor is a very significant threat. Training
of staff, contractors, and vendors are essential for maintaining the proper
level of security. The best systems are those which operate under strict
policies and procedures while security is everyone’s job.
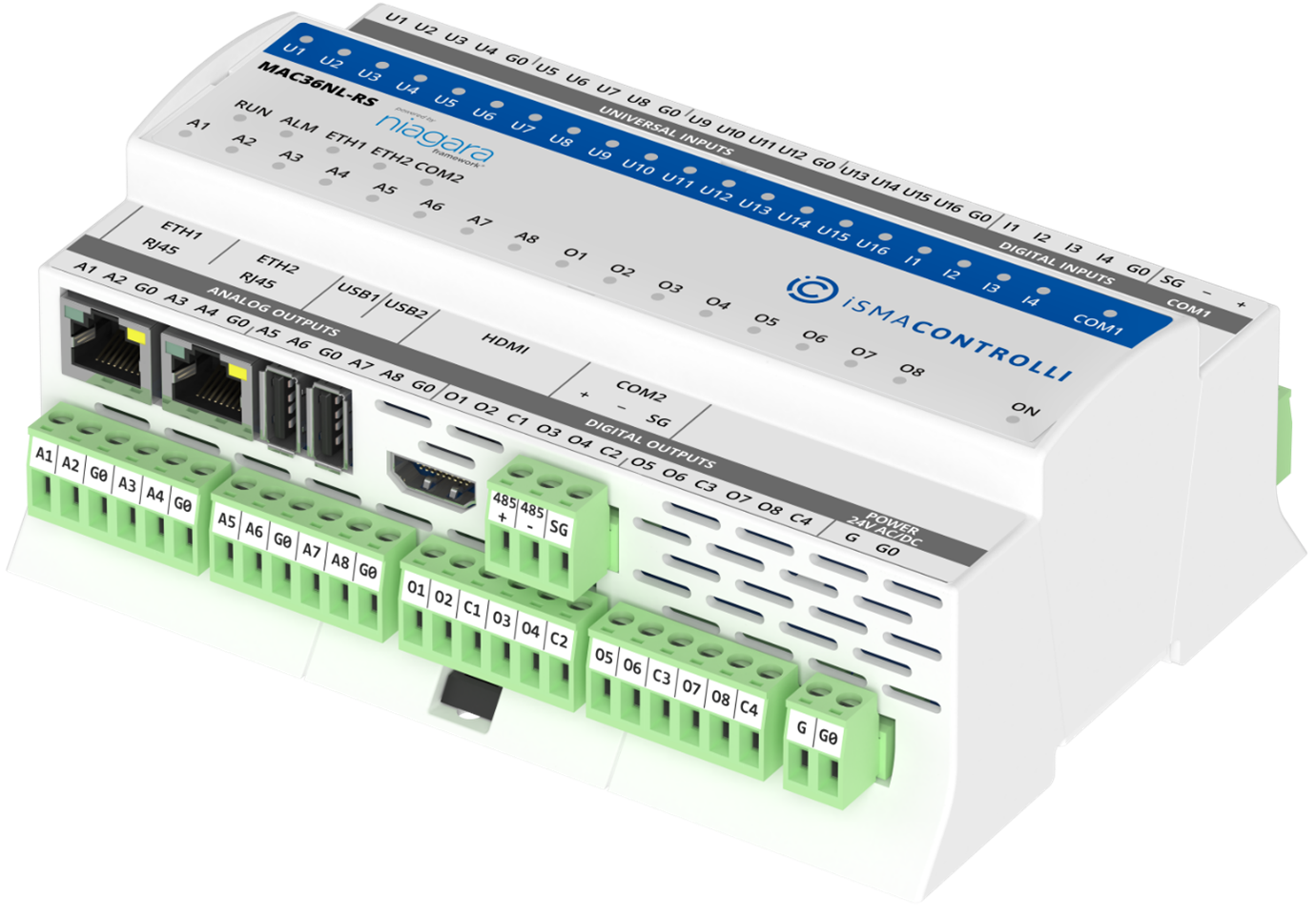
Also,
important to remember that the most vulnerable systems are those which have been
installed 20 or more years ago. Sometimes the controllers are not supported
properly by the manufacturers, just because the technology is so old that it
just can not be upgraded to the latest security standards. In such cases,
sometimes the only option to ensure security is to replace the system. Niagara Framework-based
controllers like JACE8000 or iSMA-B-MAC36NL can be a great choice
for this. Not only they are bringing the latest security standards but also have
great integration possibilities, which are required often on retrofit
buildings
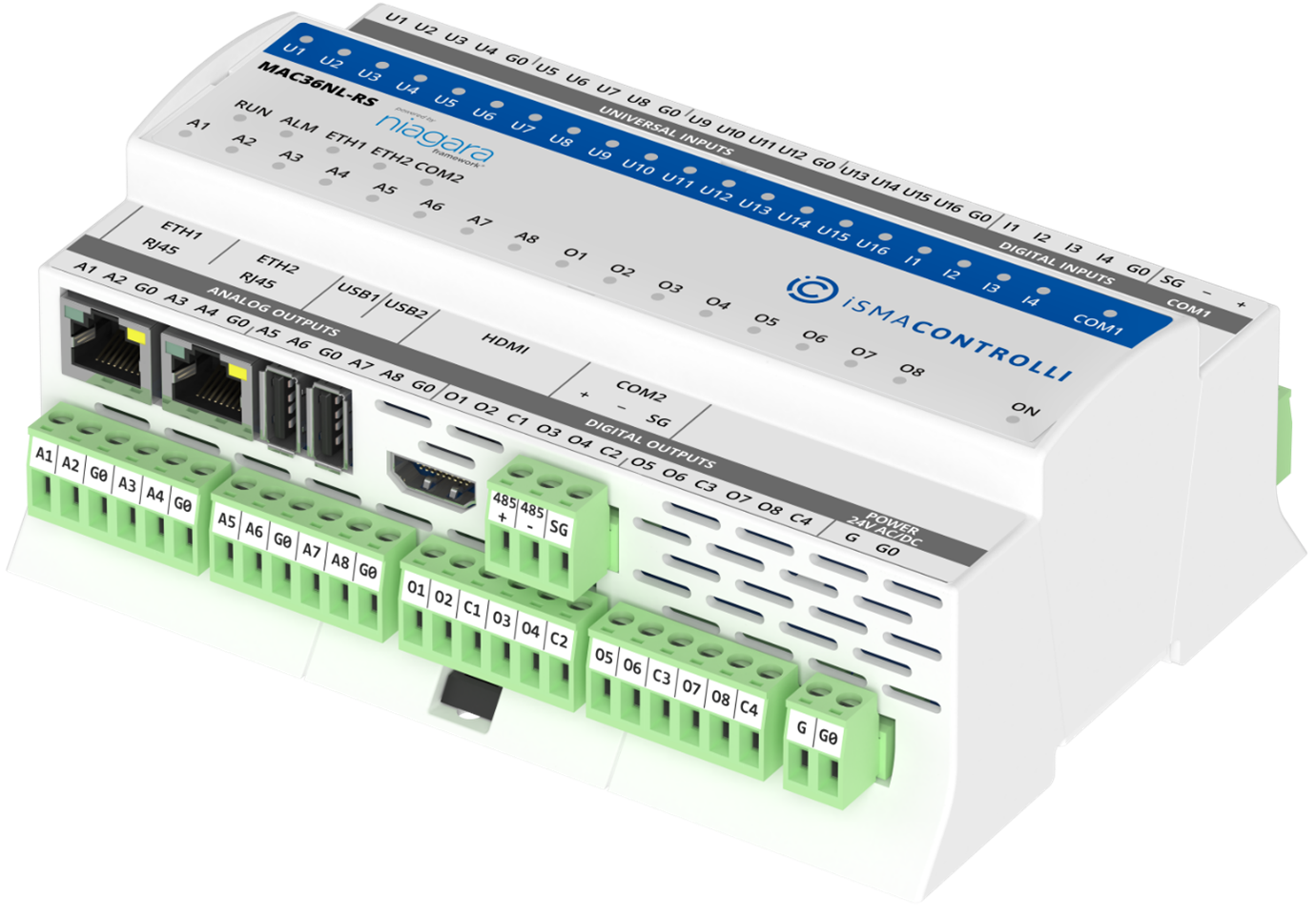 .
.
Pic.
iSMA-B-MAC36NL Hybrid IoT Controller is the winner of the Innovation Awards at
AHR EXPO 2022 in the Building Automation category
Remember
that you have to be proactive when it comes to ensuring the security of the BMS
system. Do the upgrades, check the passwords, and have a security incident
response plan in place. Always be ready for tomorrow’s surprising challenges.
About the author:
Oleksandr Zdir is a Digital
Content Specialist at iSMA CONTROLLI. His previous experience as a Product
Manager, Technical Support Engineer and System Integrator gave him a strong
understanding of the building automation market, client needs and key players. Technology
geek. Ecological volunteer. True-born engineer.
footer
[an error occurred while processing this directive]
[Click Banner To Learn More]
[Home Page] [The
Automator] [About] [Subscribe
] [Contact
Us]
 .
.